-
Six-phase integrated operations center roadmap shown as steps from governance and operating model to integration, build, readiness, and continuous improvement
Integrated Operations Center Roadmap: Proven 6-Phase Framework
An integrated operations center roadmap is a structured framework for planning, designing, implementing, and improving a modern control room. It aligns governance, operator workflows, incident management procedures, and enabling technologies such as PSIM, video management systems, access control, and building management systems into a single, coordinated operating model.
Organizations use this roadmap to move from fragmented monitoring environments toward a centralized, real-time operations capability that improves situational awareness, response effectiveness, and decision-making. Whether supporting a construction project, a large facility, or a multi-site operation, a clear roadmap reduces risk and ensures that systems, processes, and people work together from day one.
This guide presents a proven 6-phase framework for developing an integrated operations center—from initial strategy and governance through to operational readiness and continuous improvement.
Planning an integrated operations center? You can request a focused review of your roadmap, control room design, or PSIM integration strategy to identify key risks and improvement areas.
Integrated Operations Center Roadmap: 6 Phases Overview
The six phases of the integrated operations center roadmap are summarized below:
| Phase | Objective | Main Output |
|---|---|---|
| Phase 1 | Define governance and authority | Scope, decision rights, incident taxonomy |
| Phase 2 | Design the operating model | Roles, shift model, procedures, escalation logic |
| Phase 3 | Define architecture and integrations | Functional requirements, PSIM/VMS/BMS integration model |
| Phase 4 | Build and validate the solution | Configured systems, test records, defect log |
| Phase 5 | Prepare for live operations | Training, exercises, readiness criteria |
| Phase 6 | Improve performance continuously | KPIs, review cycles, optimization backlog |
Why an Integrated Operations Center Roadmap Matters
Many organizations attempt to “build a control room” by buying screens, radios, cameras, or a PSIM platform and hoping that integration automatically creates capability. In reality, technology amplifies whatever operating model already exists. If governance, procedures, decision rights, and escalation logic are unclear, even the best platform will simply make confusion faster and more visible.
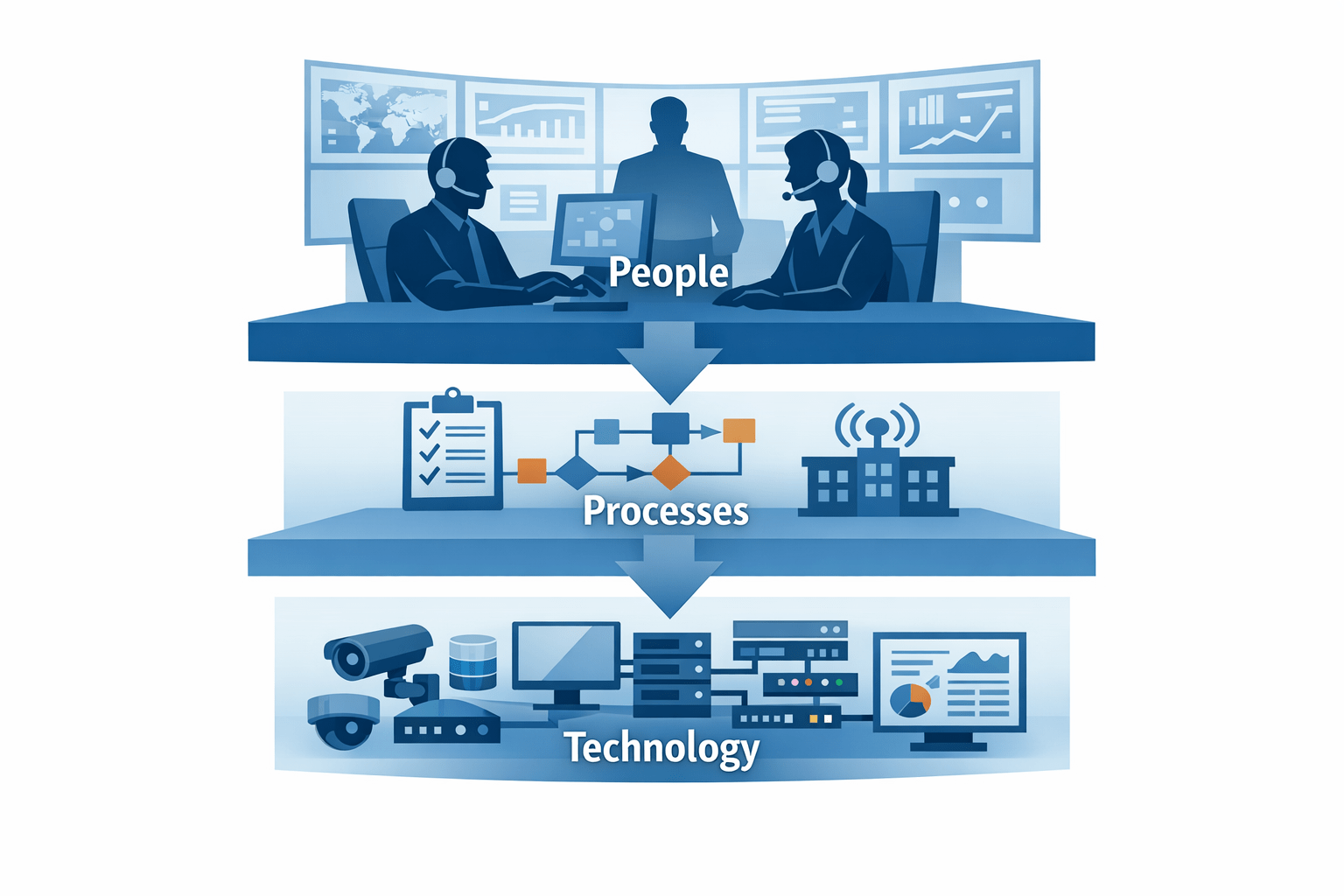
The purpose of an Integrated Operations Center Roadmap is to align people, process, and technology into a repeatable system of work that performs during routine operations and remains stable during stress, disruption, and crisis.
When the roadmap is applied correctly, the control room becomes a dependable “operating system” for situational awareness, response coordination, incident documentation, and continuous improvement.
This matters most in environments where the risk profile shifts over time. Construction introduces frequent change, temporary infrastructure, many contractors, and elevated safety risk. Early operations introduces occupancy, service commitments, and brand expectations.
Event mode introduces peak density, intense media scrutiny, and tighter authority interfaces. A roadmap allows you to design once and scale responsibly through each stage.
Scope and Operating Context
An integrated operations center typically coordinates across multiple domains. At minimum, it covers security operations such as access control, surveillance, alarm monitoring, and guard force coordination. In integrated environments, it often also manages facility events such as BMS alerts, power resilience, lifts and escalators, and fire/life safety system states.
More mature models extend to safety coordination, traffic management, environmental thresholds, planned events, and business continuity interfaces.
Before you begin, define your operating context clearly. A control room serving an active construction zone is fundamentally different from one serving a hospitality venue, an industrial site, or a public event. Your Integrated Operations Center Roadmap phases remain consistent, but the priority order, stakeholder set, and performance targets will differ. The rule is simple: the more complex the operating environment, the more you must lead with governance and operational design rather than technology.
A useful check is to ask one question:
“If all automation failed for two hours, could the team still operate safely and consistently?”
If the answer is unclear, your operating model and procedures need to mature before you add more tooling.
Integrated Operations Center Roadmap Overview: Six Phases
The roadmap below is structured in six phases. These phases reflect practical sequencing used in successful integrated control room deployments where outcomes are prioritized over tool acquisition. Some organizations will run phases in parallel, but the dependency chain should remain intact: operational intent drives procedures, procedures drive functional requirements, and requirements drive technology configuration.
In plain terms, your goal is to define how decisions are made, how work is executed, how information is captured, and how outcomes are measured. Then you configure technology to support those decisions, not to replace them. This ensures the control room is auditable, defensible, and resilient.
Skipping straight to Phase 3 (Technology) without a Phase 1 ConOps is the #1 reason PSIM and Integrated Control Room projects exceed budgets and fail to meet operational goals.
- Phase 1: Governance and operational intent
- Phase 2: Operating model, roles, and procedures
- Phase 3: Technology architecture and integration
- Phase 4: Build, configure, and validate
- Phase 5: Readiness, exercises, and transition to operations
- Phase 6: Steady-state operations and continuous improvement
Phase 1: Strategy and Governance Definition
The first phase of the integrated operations center roadmap establishes the governance and strategic foundation for all subsequent design and implementation decisions. It defines how decisions are made, who holds authority, and how incidents are classified and escalated across the organization.
Objectives of Phase 1
- Define the mission, scope, and applicability of the integrated operations center
- Establish governance structures and decision-making authority
- Develop a consistent incident classification and escalation model
- Align stakeholders across departments and external authorities
- Initiate the formal Concept of Operations (ConOps) to act as the single source of truth for operational intent.
Key Tasks
- Conduct stakeholder alignment workshops across security, facilities, and operations
- Define governance principles, decision rights, and escalation ownership
- Develop an incident and event taxonomy with severity levels and response objectives
- Initiate the Concept of Operations (ConOps)
- Identify regulatory and authority notification requirements
Governance and Incident Taxonomy
Governance is the foundation of every credible control room program. It answers three non-negotiable questions: who decides, on what basis, and with what authority. In integrated environments, governance must also resolve boundary issues between departments, vendors, and external authorities. Without a governance model, operators escalate inconsistently, supervisors improvise, and reports become incomparable over time.
Start by defining the mission, scope, and applicability across project phases. Then define a classification and escalation model that is simple enough to execute consistently. If you operate in a jurisdiction where authorities have defined notification requirements, embed those requirements into escalation logic as mandatory steps. Where requirements are unclear, document the assumptions, identify the gaps, and assign an owner to close them.
A critical governance artifact is the incident and event taxonomy. This is not a list of “possible incidents.” It is a structured model defining categories, sub-categories, severity levels, ownership, response objectives, escalation triggers, and closure criteria. A strong taxonomy becomes the backbone for PSIM configuration, reporting, performance management, and training.
If you publish or support a formal Concept of Operations, this is the phase where it should be initiated. The governance scope, mission, incident taxonomy, and escalation model are defined here and form the ConOps foundation. The document will be refined and completed as subsequent phases of the integrated operations center roadmap add the operating model, procedures, and technology design. Treat it as a living document that matures alongside the roadmap.
In jurisdictions like the UAE, the taxonomy must explicitly account for SIRA or Civil Defence notification triggers to ensure legal and regulatory compliance from day one.
Common Mistakes to Avoid
- Starting with technology selection before defining governance and operational requirements
- Lack of clear ownership and decision authority
- Overcomplicating the incident taxonomy, making it difficult to apply consistently
- Ignoring regulatory or authority notification requirements
Phase 2: Operating Model Design
With governance established, Phase 2 of the integrated operations center roadmap defines how the control room works day to day. This is where many projects fail by skipping directly to tool configuration. An integrated operations center requires a clear operating model covering shift coverage, supervision ratios, skill mix, escalation ownership, and the relationship between control room staff and field teams. It also requires a business-as-usual model that continues to function during busy periods rather than degrading under pressure.
Objectives of Phase 2
- Define how the integrated operations center operates on a daily basis
- Establish clear roles, responsibilities, and supervision structures
- Design repeatable workflows for routine operations and incident response
- Align procedures, staffing, and escalation logic with the governance model established in Phase 1
- Phase 2 translates the high-level mission defined in the ConOps (Phase 1) into the specific human workflows required to achieve it.
Key Tasks
- Define operator, supervisor, and management roles within the control room
- Set shift coverage, supervision ratios, and required skill mix
- Define the relationship between control room staff and field teams
- Separate routine procedures from time-critical response procedures
- Design workflows that operators can execute consistently under normal and high-pressure conditions
- Define required operator actions within integrated systems, not only in the physical environment
Operating Model, Roles, and Workload
An operating model must be practical, executable, and resilient. This means defining who does what, when, and with what authority. Operators, supervisors, and field teams should not rely on informal habits or personal interpretation to decide who owns a task or when a situation should be escalated. Ambiguity at this stage leads to delays, duplicated effort, and inconsistent outcomes.
Staffing design should reflect both normal operating demand and surge conditions. This includes shift coverage, supervision ratios, skill mix, and contingency arrangements for periods of high activity. In integrated environments, operators may be required to manage security, safety, facilities, and operational events in parallel, so workload balancing and prioritization rules must be built into the operating model from the start.
Difference between Standard Operating Procedures and Response Procedures
Procedures should be separated into two families. Standard Operating Procedure (SOP) development defines routine tasks such as shift handover, system health checks, patrol coordination, access management, reporting, and daily situational awareness. Response Procedures define time-critical workflows for incidents such as fire alarms, medical emergencies, intrusions, utility failures, or public disorder.
Treating these procedure types as the same creates long, vague documents and inconsistent execution. Standard tasks and emergency response require different levels of urgency, structure, and decision support. Separating them makes the operating model easier to train, audit, and improve.
Once these procedure types are clearly defined, the next step is to design them in a way that operators can execute consistently under real operating conditions.
Procedure Design for Real Operations
Procedure design should follow operational language that operators can execute under stress. Each response procedure should define triggers, verification steps, minimum information requirements, escalation thresholds, communications templates, and closure criteria. A procedure that reads well in a workshop but cannot be applied during a live incident is not operationally useful.
Where integrations exist, define what the operator should see and what actions are required in the system, not just in the physical world. This is how you move beyond screen watching and toward reliable human-system interaction. Integrated platforms should support decision-making, not replace the need for clear procedure design.
Effective procedure design reduces the cognitive load on operators during a crisis, ensuring that integrated systems provide decision support rather than data overload.
Key Deliverables
- Operating model definition including roles, responsibilities, and authority levels
- Shift coverage model, supervision ratios, and staffing assumptions
- Routine SOP structure and response procedure framework
- Defined workflows between control room staff and field teams
- Operator action requirements for integrated systems and alarm handling
Common Mistakes to Avoid
- Skipping operating model design and moving directly into system configuration
- Combining routine procedures and incident response into one vague document set
- Defining procedures without considering stress, workload, and surge conditions
- Failing to define what operators must do inside the system as well as in the field
Control Room and Security Operations Center Design
Control room and security operations center design is often misunderstood as a question of room layout, screens, or technology selection. In practice, effective design starts with the operating model and translates it into a working environment that supports decision-making, communication, and coordination under real conditions.
The outputs from Phase 1 and Phase 2 define the foundation of this design. Governance determines who makes decisions and how escalation is managed. The operating model defines roles, workflows, supervision, and interaction between control room staff and field teams. These elements shape how the control room must function before any technology or physical layout is finalized.
A well-designed control room aligns people, processes, and systems. Operator positions, screen layouts, alarm handling logic, and communication channels should reflect the workflows that operators are expected to execute. This ensures that the environment supports consistent response rather than relying on individual interpretation or workarounds.
This is particularly important when comparing integrated operations centers with traditional security operations centers. A physical security operations center may focus primarily on alarm monitoring and incident response, while an integrated operations center requires coordination across security, safety, facilities, and operational domains. The design must therefore support multi-domain visibility and shared decision-making.
Once these design principles are clearly defined, they can be translated into system architecture and integration requirements. This is the transition point where operational intent becomes technical design, which is addressed in the next phase of the integrated operations center roadmap.
Phase 3: Technology Architecture and Integration
Technology should be designed as an enabling layer within the integrated operations center roadmap. The architecture must support the operating model defined in previous phases, rather than driving it. At this stage, organizations define system boundaries, integrations, data flows, retention requirements, and failover expectations to ensure reliable and scalable operations.
Objectives of Phase 3
- Define the overall control room architecture and system boundaries
- Align technology design with governance, workflows, and operating model
- Ensure resilience through redundancy, failover, and degraded mode planning
Key Tasks
- Map data flows between systems and define integration requirements
- Confirm readiness for PSIM or orchestration platforms
- Establish data retention, audit, and reporting requirements
- Define degraded mode operations and failover scenarios
Architecture Layers and System Integration
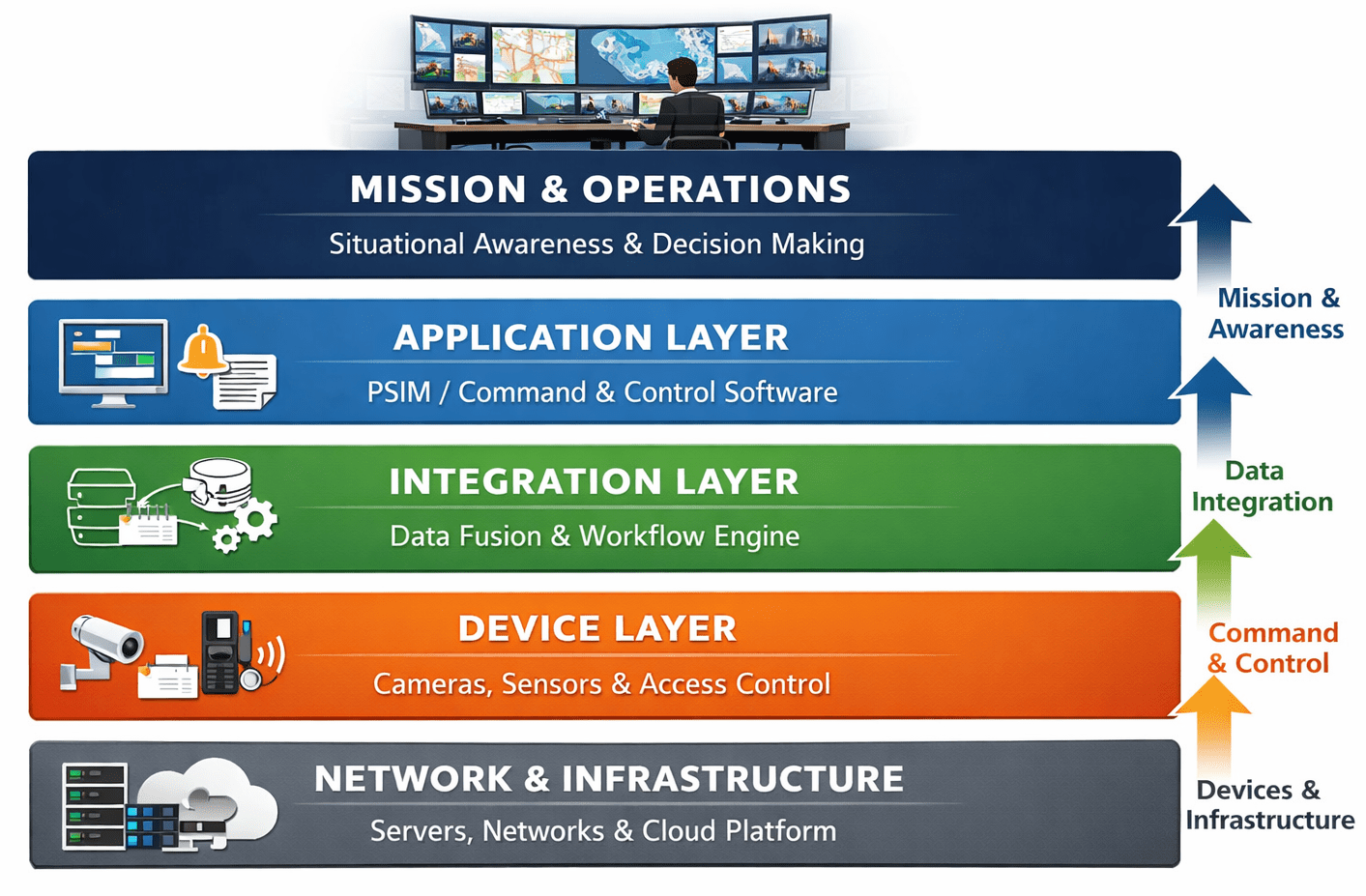
A practical architecture separates the environment into layers. The field layer includes CCTV, access control, intrusion detection, fire systems, building management systems, environmental sensors, and any specialized systems. These systems generate the events that form the basis of control room operations.
The integration layer normalizes and correlates events, typically through PSIM or incident orchestration tooling. This layer enables operators to manage incidents consistently across multiple systems rather than switching between isolated interfaces.
The communications layer covers radio, push-to-talk, telephony, public address, and authority notification interfaces. Effective communication design ensures that information flows quickly between the control room, field teams, and external stakeholders during incidents.
The analytics layer supports incident logging, dashboards, reporting, and performance monitoring, with a strong emphasis on auditability and traceability. This layer enables continuous improvement and performance management across the integrated operations center.
PSIM Integration Strategy
Before defining PSIM workflows, confirm that the operational foundation is stable. Incident categories must be defined, escalation logic must be agreed, operators must understand what decisions they are expected to support, and management must know what information it needs during incidents.
If these conditions are not yet met, PSIM configuration will encode unresolved questions rather than enforce good practice. Once the foundation is solid, define the incident lifecycle model clearly and map workflows to system integrations. In this way, PSIM supports the operating model rather than attempting to define it.
Resilience and Degraded Mode Operations
Define degraded mode operations explicitly. Systems will fail, networks will degrade, and integrations may break after upgrades or configuration changes. The operating model must account for these scenarios.
Operators must know how to operate safely when the platform is unavailable or partially available. Degraded mode steps should be embedded into both SOPs and response procedures and must be tested during readiness exercises to ensure reliability under real conditions.
Key Deliverables
- Control room architecture definition including system layers and boundaries
- Integration and data flow diagrams
- PSIM or orchestration platform requirements and workflow mapping
- Data retention, reporting, and audit requirements
- Degraded mode and failover procedures
Common Mistakes to Avoid
- Designing technology before finalizing the operating model and governance
- Implementing PSIM without a clear incident taxonomy and escalation logic
- Over-integrating systems without clear operational value
- Ignoring degraded mode and failover scenarios
For a general overview of Physical Security Information Management, see Physical Security Information Management (PSIM).
Phase 4: Build, Configure, and Validate
Phase 4 of the integrated operations center roadmap converts defined requirements into an operational system. This is where governance, operating model, and technology architecture are implemented, configured, and tested to ensure they function together as a cohesive control room environment.
Objectives of Phase 4
- Configure systems to support the defined operating model and workflows
- Implement incident lifecycle management across all integrated platforms
- Validate that operators can execute response procedures effectively in real scenarios
- Ensure data structure supports reporting, analytics, and audit requirements
Key Tasks
- Configure incident lifecycle workflows including detection, verification, classification, response, coordination, and closure
- Implement severity logic, escalation rules, and automated actions
- Define operator layouts, dashboards, and alarm handling rules
- Standardize incident log fields, reporting structures, and closure codes
- Conduct functional and operational testing under realistic conditions
System Configuration and Workflow Implementation
This phase converts requirements into an operational configuration and aligns system build activities with a structured control room maturity roadmap. For PSIM implementations, that means configuring the full incident lifecycle — detection, verification, classification, response, coordination, and formal closure — through incident types, severity logic, correlation rules, automated actions, checklists, and escalation workflows.
The goal is to reduce cognitive load and enforce consistent decision-making without making the system rigid or unrealistic. Configuration should support operators in executing procedures efficiently rather than introducing unnecessary complexity.
Operational Validation and Testing
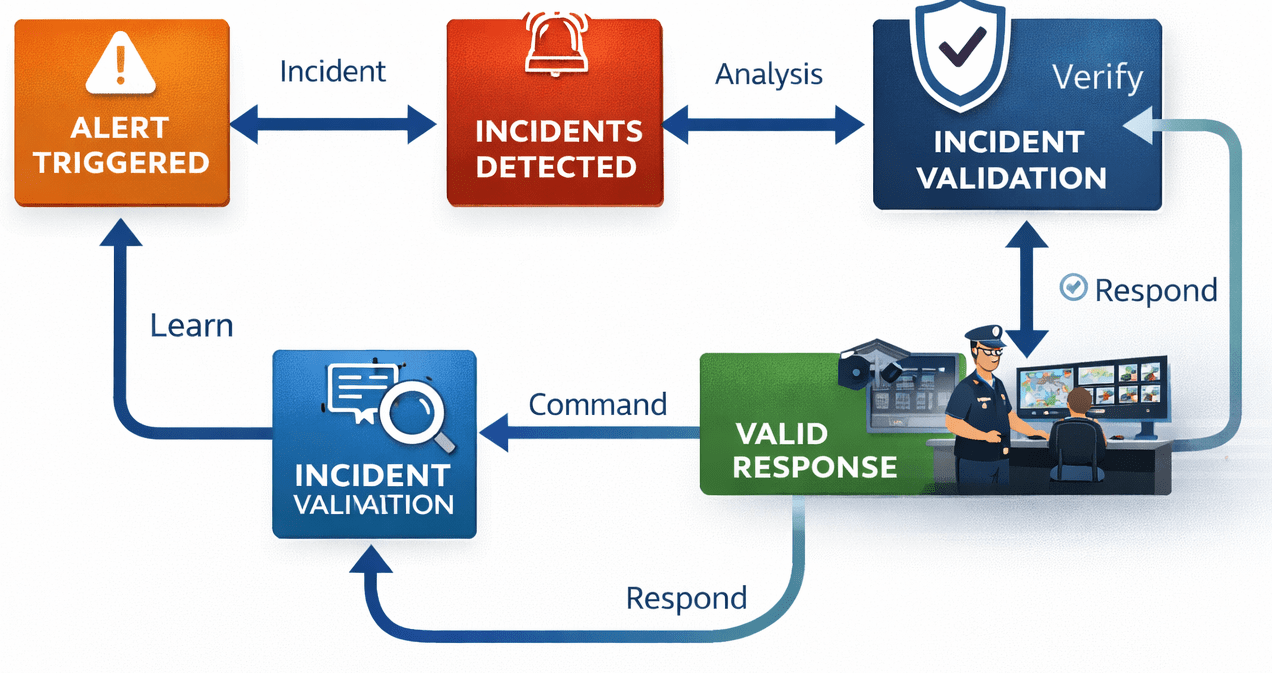
Validation must be operational, not just technical. It is not sufficient to show that an alarm appears on screen. You must demonstrate that operators can classify events correctly, obtain required information, escalate appropriately, coordinate field response, and close incidents with a complete and accurate record.
Testing should include realistic conditions such as high alarm volumes, concurrent incidents, and degraded mode scenarios. This ensures that the system performs reliably under real-world pressure, not just in controlled test environments.
Reporting and Data Structure
Ensure that reporting is designed during the build phase, not after go-live. If incident records are not structured, performance analytics will be weak and inconsistent. Define mandatory fields, standardized narratives, evidence attachment rules, and closure codes early in the configuration process.
Well-structured data enables meaningful trend analysis, supports audit readiness, and provides the foundation for continuous improvement in later phases of the integrated operations center roadmap.
Key Deliverables
- Configured systems supporting incident lifecycle and workflows
- Operator dashboards, layouts, and alarm handling configurations
- Test plans and validation scenarios including degraded mode testing
- Structured incident reporting framework and data model
- Defect logs and validation records
Common Mistakes to Avoid
- Focusing on technical configuration without validating operational usability
- Testing systems in isolation without realistic operational scenarios
- Designing reporting after go-live instead of during configuration
- Overcomplicating workflows, increasing operator workload and error risk
Control Room Implementation Strategy
A control room implementation strategy ensures that the transition from design to live operations is structured, controlled, and aligned with operational objectives. It defines how systems, procedures, and people are brought together in a coordinated way rather than implemented in isolation.
Implementation is not a single step, but a sequence of activities that must follow the logic established in the integrated operations center roadmap. Governance, operating model, and procedures should already be defined before systems are configured. Technology is then implemented to support these foundations, not to replace them.
A practical implementation strategy includes configuration, testing, validation, and staged deployment. Systems should be introduced in a controlled manner, with clear acceptance criteria and defined responsibilities. This reduces risk and ensures that issues are identified early rather than during live operations.
Equally important is the alignment between technical implementation and operational readiness. Operator workflows, escalation logic, and reporting structures must be reflected in system configuration. Without this alignment, even well-designed systems can lead to inconsistent execution and increased workload.
A structured control room implementation strategy therefore connects design, configuration, validation, and readiness into a single process. This ensures that the control room is not only technically functional, but operationally effective from the first day of live operations.
Phase 5: Readiness, Exercises, and Transition to Operations
Phase 5 of the integrated operations center roadmap ensures that the control room is ready for live operations. At this stage, systems, procedures, and people are brought together and tested under realistic conditions to confirm that the integrated operations center can function effectively in real scenarios.
Objectives of Phase 5
- Validate that operators can execute procedures in real-world conditions
- Prepare teams for both routine operations and major incidents
- Ensure a structured transition from project delivery to live operations
- Establish governance, review cycles, and operational routines
Key Tasks
- Deliver role-based and scenario-based training for operators and supervisors
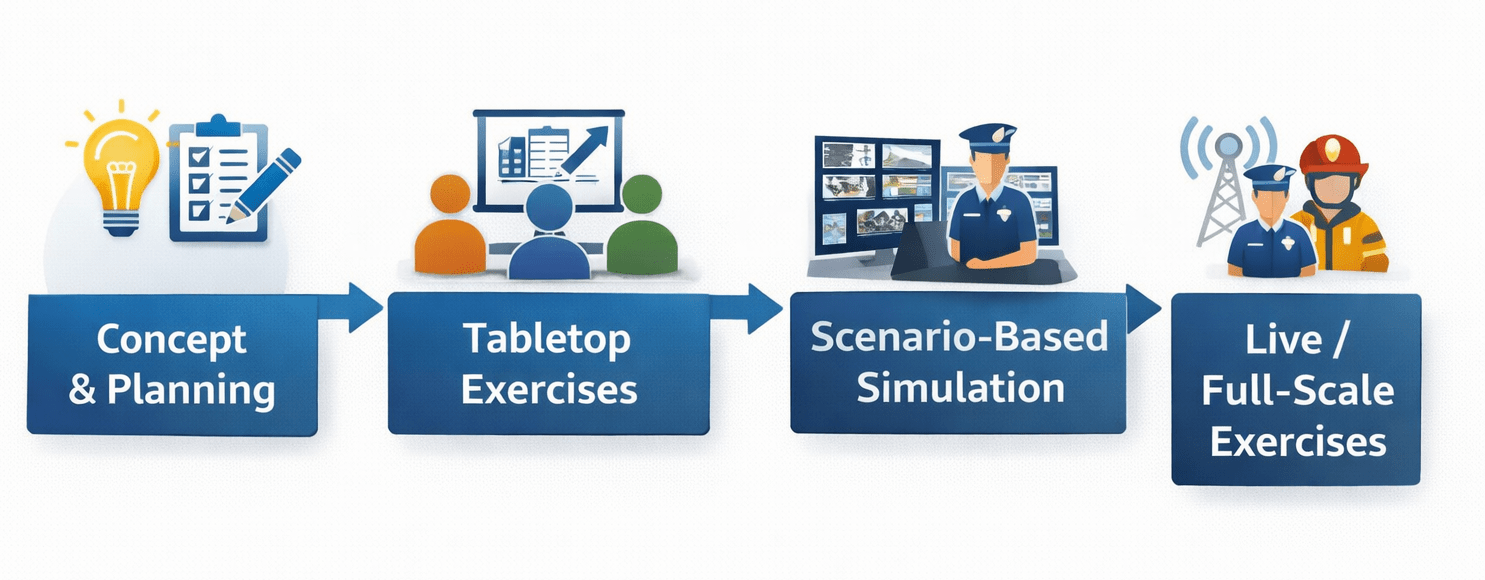
- Conduct tabletop exercises followed by simulation-based scenarios
- Test communication flows, escalation logic, and authority notifications
- Validate reporting quality, documentation, and incident closure processes
- Plan and execute transition from project team to operations team
- Engage external authorities or stakeholders where required
Training and Operational Exercises
Readiness is where you prove that the control room works with real people, not just configured systems. Training should be role-based and scenario-based, covering both normal operations and major incident coordination. Operators must understand not only how to use the system, but how to make decisions within defined control room procedures and escalation frameworks.
Exercises should start with structured tabletop walkthroughs and progress to simulations that test communications, authority notifications, decision speed, and documentation quality. Scenarios should reflect realistic conditions, including concurrent incidents and degraded system availability.
Transition to Operations
Transition to operations requires disciplined handover from the project team to the operations team. This includes technical handover of systems, access permissions, vendor support processes, and spares management, as well as operational handover of control room procedures, training records, and reporting responsibilities.
A well-managed transition also establishes governance structures for live operations, including routine meetings, escalation oversight, and a defined cadence for reviewing and improving procedures and performance.
Coordination with External Authorities
Where external authorities are part of the response model, readiness should include joint engagement, even if only through structured liaison and notification testing. This reduces friction during real incidents and ensures that the integrated operations center aligns with authority expectations.
Readiness Criteria
Before go-live, define clear readiness criteria that must be met. This may include successful completion of training, validated exercise performance, confirmed system functionality, and complete documentation. Readiness should be formally assessed rather than assumed.
Key Deliverables
- Training materials and training completion records
- Exercise plans, scenarios, and evaluation results
- Transition plan and handover documentation
- Defined governance structure for live operations
- Readiness assessment and go-live approval
Common Mistakes to Avoid
- Assuming readiness without structured testing and validation
- Focusing on system training without scenario-based exercises
- Rushing transition without clear handover of responsibilities
- Failing to involve external authorities or stakeholders in readiness activities
Phase 6: Steady-State Operations and Continuous Improvement
Phase 6 of the integrated operations center roadmap focuses on performance management and continuous improvement after go-live. At this stage, the control room operates as a stable function and shifts from implementation to measuring outcomes, identifying trends, and refining operations over time.
Objectives of Phase 6
- Establish a structured performance management framework
- Measure operational effectiveness using defined KPIs
- Continuously improve procedures, training, and system use
- Ensure long-term stability and stakeholder confidence
Key Tasks
- Define and monitor KPIs across detection, response, resolution, and compliance
- Conduct daily, weekly, and periodic operational reviews
- Analyze incident data, trends, and near-miss reports
- Update procedures, training materials, and workflows based on evidence
- Implement version control and communication processes for updates
- Prepare for peak-load and event-based operational scenarios
Performance Management and KPI Framework
After go-live, the goal shifts from implementation to performance management. Mature control rooms measure outcomes, identify trends, and adjust controls. This requires a disciplined KPI model covering detection, response, resolution, compliance, and stakeholder impact where relevant.
It also requires structured reviews, including daily situation assessments, weekly trend reviews, and periodic governance forums. These review cycles ensure that performance is continuously monitored and that issues are identified early.
Continuous Improvement and Learning
Continuous improvement should be evidence-based. Use incident logs, near-miss reports, and audit findings to refine procedures and training. Ensure that changes are version-controlled and communicated consistently across all shifts.
The most mature programs institutionalize learning. They treat every major incident, exercise, and system outage as an input to improvement. Over time, this produces a control room that is more stable, more predictable, and more trusted by stakeholders and authorities.
Event and Peak-Load Operations
If your organization supports planned events or peak-load periods, implement an event-mode overlay. This may include additional staffing, adjusted escalation thresholds, dedicated communications channels, and enhanced situational reporting to maintain control during periods of increased demand.
Key Deliverables
- KPI framework and performance dashboards
- Regular review reports and governance meeting outputs
- Updated procedures and training materials
- Version-controlled documentation and change logs
- Event-mode operational plans
Common Mistakes to Avoid
- Failing to define measurable KPIs for performance management
- Conducting reviews without translating findings into improvements
- Updating procedures without proper version control or communication
- Ignoring peak-load or event-based operational requirements
Integrated Operations Center vs Physical Security SOC vs GSOC vs Traditional Control Room
Organizations often use terms such as integrated operations center (IOC), security operations center (SOC), and global security operations center (GSOC) interchangeably, but they are not the same. In many industries, SOC is increasingly associated with cybersecurity monitoring. In this article, the comparison is focused on the physical security and integrated operations context, where the scope, workflows, and operating model differ significantly from a cyber SOC.
Key Differences at a Glance
| Type | Primary Focus | Scope | Typical Use Case |
|---|---|---|---|
| Integrated Operations Center (IOC) | Multi-domain coordination | Security, safety, facilities, and operational monitoring | Complex sites, campuses, mixed-use developments, smart environments |
| Physical Security Operations Center (SOC) | Security monitoring and incident response | Alarms, CCTV, access control, dispatch, and security escalation | Enterprise security, critical infrastructure, site protection |
| Global Security Operations Center (GSOC) | Centralized multi-site risk oversight | Regional or global security awareness, crisis coordination, travel risk, executive support | Multinational organizations and distributed operations |
| Traditional Control Room | Single-domain monitoring and control | Process systems, building systems, or one operational discipline | Utilities, industrial plants, transport, and facility operations |
Integrated Operations Center (IOC)
An integrated operations center combines multiple operational domains into one coordinated environment. It brings together security, safety, facilities management, and operational monitoring so that incidents can be assessed and managed through a shared operating model rather than through isolated teams or disconnected systems. The value of an IOC is not only visibility, but coordinated decision-making across functions.
Physical Security Operations Center (SOC)
In the physical security context, a security operations center is primarily focused on security events such as alarms, intrusions, suspicious activity, access control exceptions, dispatch coordination, and incident escalation. It is usually narrower in scope than an IOC because it does not fully integrate broader facilities or operational workflows. This is different from a cyber SOC, which is centered on digital threats, network monitoring, and cybersecurity incident response.
Global Security Operations Center (GSOC)
A GSOC extends security coordination across multiple sites, regions, or countries. Its role is usually less about detailed site-level control room execution and more about centralized situational awareness, escalation management, crisis coordination, travel risk monitoring, and support to senior decision-makers. A GSOC may receive information from local SOCs or control rooms rather than replacing them.
Traditional Control Room
A traditional control room is normally designed around one operational discipline, such as industrial process control, utilities management, building systems, or transport operations. It may be highly capable within that domain, but it does not necessarily provide integrated workflows across security, safety, facilities, and wider operational coordination.
Why the Difference Matters
The key distinction is not the room itself, but the degree of operational integration. A physical security SOC improves security monitoring and response. A GSOC improves centralized oversight across locations. A traditional control room supports one operational domain. An integrated operations center goes further by aligning governance, procedures, staffing, escalation logic, and enabling technology across multiple domains in one coordinated model.
In practice, many organizations evolve toward an integrated operations center when complexity increases and incidents begin to cross functional boundaries. That shift usually happens when security, facilities, safety, and operational issues can no longer be managed effectively through separate workflows or separate teams.
Integrated Operations Center Roadmap Deliverables and Evidence
An effective integrated operations center roadmap should produce tangible, verifiable deliverables. If your program cannot demonstrate these artifacts, it is likely relying on informal knowledge and will degrade over time, particularly with staff turnover or organizational change.
Core Deliverables You Should Expect
- Concept of Operations (ConOps)
- Procedure library including SOPs and response procedures
- Incident and event taxonomy
- Training matrix and competency framework
- KPI dashboard with structured performance metrics
Technology and Integration Deliverables
- Control room architecture diagram
- System integration matrix
- Incident workflow configuration (e.g. PSIM or orchestration platform)
- Test plans and validation documentation
- Degraded mode procedures and failover scenarios
Governance and Operational Deliverables
- Scope definition and mission statement
- RACI matrix and decision authority model
- Escalation matrix and authority interface map
- Daily reporting model and KPI definitions
- Audit schedule and continuous improvement log
Readiness and Transition Deliverables
- Training records and certification tracking
- Exercise plans and evaluation reports
- Corrective action tracking
- Transition and handover documentation
These deliverables provide the foundation for consistency, auditability, and continuous improvement. They ensure that the integrated operations center operates as a structured system rather than relying on individual knowledge or informal practices.
Common Failure Modes in Integrated Operations Centers (and How to Avoid Them)
Control room programs tend to fail in predictable ways. Understanding these failure modes helps organizations avoid costly redesign, operational gaps, and inconsistent performance.
Common Failure Modes
- Treating technology procurement as the starting point instead of defining governance and operating model first
- Developing procedures that are too long, too abstract, or not written for execution under stress
- Failing to define decision rights, leading to inconsistent escalation and delayed response
- Overcomplicating system integration without clear operational benefit
- Neglecting degraded mode operations and failover scenarios
- Assuming readiness without realistic testing and validation
How to Avoid These Failures
These risks can be mitigated by following the correct sequencing of the integrated operations center roadmap. Governance should be defined first, followed by operating model and procedures. Technology should then be configured to support these foundations, not replace them.
Testing must be conducted under realistic conditions, including high workload scenarios and degraded system availability. Finally, structured governance and continuous improvement processes must be established to ensure that the control room evolves over time rather than stagnates.
Strategic Implementation Support
Translating an Integrated Operations Center roadmap into a resilient, site-specific model requires more than just software—it requires a bridge between Governance and Technology.
I provide hands-on services to ensure your roadmap is executable, including:
- Developing a formal Concept of Operations (ConOps)
- Building structured, audit-ready SOP and Response libraries
- Defining PSIM functional workflows and escalation logic
- Ensuring operational readiness through stress-testing and exercises
Ready to review your roadmap or implementation approach?
Frequently Asked Questions About Integrated Operations Center Roadmaps
What is an integrated operations center roadmap?
An integrated operations center roadmap is a structured framework for building and improving a control room capability. It sequences governance, operating model design, procedures, technology integration, readiness validation, and continuous improvement into a repeatable lifecycle.
Is PSIM required to implement an integrated operations center?
No. PSIM can support orchestration and event correlation, but it is not the foundation. Governance, procedures, and the operating model must be defined first. Many organizations start with structured workflows and reporting before introducing PSIM once requirements are stable.
How do you define success for a modern control room?
Success is measured through outcomes such as reliable detection, consistent escalation, timely response, complete documentation, and defensible audit trails. Mature programs also track trend reduction, compliance improvement, and stakeholder confidence.
What is the biggest risk when transitioning from construction to early operations?
The main risk is carrying temporary construction-phase assumptions into permanent operations. Construction environments often rely on informal coordination and rapid change, while early operations require stable procedures, repeatable reporting, and clearly defined authority interfaces. A structured transition plan is essential.
What should be included in degraded mode operations?
Degraded mode operations should define how operators verify alarms, communicate, escalate, dispatch, and document incidents when systems are partially or fully unavailable. This includes fallback tools, manual logging procedures, and system restoration steps. These scenarios must be tested during exercises.
How often should control room procedures be reviewed and updated?
Review frequency depends on operational requirements, but mature control rooms follow a structured schedule, including periodic reviews and updates after incidents or exercises. Changes should be version-controlled, approved, and communicated clearly to all shifts.
What systems are typically integrated in an integrated operations center?
Typical integrations include CCTV, access control, intrusion detection, fire and life safety systems, building management systems, environmental sensors, communications platforms, and incident management tools. These systems are combined to provide a unified operational view and coordinated response capability.
How long does it take to implement an integrated operations center?
Implementation timelines vary depending on scope and complexity, but most programs take several months to over a year. The duration depends on factors such as project size, system integration requirements, organizational alignment, and readiness maturity.
What is the difference between an integrated operations center and a security operations center?
An integrated operations center combines multiple domains such as security, safety, facilities, and operations into one coordinated environment. A physical security operations center focuses primarily on security monitoring and incident response. In many organizations, the term SOC may also refer to cybersecurity operations, which are outside the scope of a physical control room.
Is an integrated operations center the same as a control room?
No. A traditional control room usually focuses on a single domain such as building systems or industrial processes. An integrated operations center combines multiple functions and aligns them through shared procedures, workflows, and decision-making models.
When should PSIM be introduced in the roadmap?
PSIM should be introduced after governance, operating model, and procedures are clearly defined. Implementing PSIM too early can result in encoding unclear processes. A stable operational foundation ensures that PSIM supports workflows rather than defining them.
Closing Guidance
An integrated operations center is not defined by the technology it uses, but by how effectively people, processes, and systems work together under real conditions. The integrated operations center roadmap provides a structured way to achieve this by progressing through six essential phases: governance, operating model design, procedures, technology integration, readiness validation, and continuous improvement.
Each phase builds on the previous one. Skipping steps or changing the sequence often leads to inconsistent operations, unnecessary complexity, or systems that do not support real decision-making. When applied correctly, the roadmap produces a control room that is predictable, auditable, and capable of handling both routine operations and high-impact incidents.
For organizations planning new facilities or transitioning from construction to operations, this lifecycle approach is particularly important. Early decisions shape long-term performance. Building on a clear operational foundation ensures that the control room can scale, adapt, and remain effective as risks, stakeholders, and operational demands evolve.
If you are developing or reviewing an integrated operations center, focus on clarity, consistency, and execution. Define how decisions are made, design workflows that operators can apply under pressure, and ensure that technology supports rather than defines operations. This is what turns a control room into a reliable operational capability.
If you want to assess your current roadmap, operating model, or implementation approach, you can request a structured review to identify gaps, risks, and practical next steps.
Disclaimer: This content is informational and does not constitute legal advice. Regulatory requirements and licensing conditions differ by jurisdiction and must be confirmed for each site.