-
How I Approach Security Operations — and Where PSIM Truly Fits
Security Operations Strategy & PSIM Integration
Security Operations Approach PSIM: Proven Framework for Integrated Security Operations
A practical, experience-driven security operations approach using PSIM to deliver clarity, structure, and operational readiness across complex environments.
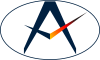
Security Operations Approach PSIM: From Complexity to Clarity
A security operations approach psim is often misunderstood as a technology solution. In reality, it is an operational framework that brings structure, clarity, and consistency to complex security environments.
Security operations rarely fail in dramatic ways. They fail quietly through confusion, hesitation, unclear ownership, and systems that generate data but do not support decisions.
When I step into a new security operations role, whether permanent or advisory, my objective is not to introduce tools or restructure teams. It is to make operations predictable, calm, and trusted.
This article explains my approach to security operations and where PSIM truly fits: not as a starting point, but as an operational enabler built on clarity, governance, and readiness.
What Is a Security Operations Approach Using PSIM?
A security operations approach PSIM is a structured method of managing security through integration, coordination, and decision support. It aligns people, processes, and technology into a single operational model that supports consistent and informed decision-making.
Rather than treating systems such as CCTV, access control, and alarms as isolated tools, PSIM connects them into one coordinated environment. This enables operators to understand incidents faster, escalate them correctly, and manage responses across multiple stakeholders.
The objective is not visibility alone. The objective is operational clarity — ensuring that every incident is understood, every decision is supported, and every action follows a predictable structure.
In this context, PSIM is not the starting point of security operations. It is the layer that enables integration once a clear operational model already exists.
Why Security Operations Break Down Without Anyone Noticing
Most organizations believe they have a security problem when they actually have an operational clarity problem. Systems may be in place, teams may be active, and reports may be generated — yet decision-making remains inconsistent.
Common symptoms include:
- Incidents handled differently depending on who is on duty
- Escalations driven by individuals rather than defined criteria
- Technology producing data instead of actionable decisions
- Operators reacting instead of coordinating
- Leadership surprised by incidents that were visible but not understood
None of this is caused by a lack of effort. It is caused by the absence of a shared operational model.
Without a structured framework such as a phased integrated operations center approach, organizations often invest in tools before defining how decisions should be made.
Before procedures, dashboards, or integrations are introduced, security operations need a clear definition of normal. Only then can escalation, coordination, and incident management become consistent and reliable.
Assessing Security Operations: The First 30–60 Days
A structured security operations approach PSIM does not begin with change. It begins with understanding how operations actually function under real conditions.
In the first 30–60 days, the focus is not on introducing new systems or procedures, but on observing how decisions are made, how information flows, and where coordination breaks down.
This assessment typically focuses on:
- How incidents are handled in practice versus how they are documented
- Who makes decisions under pressure and how those decisions are communicated
- Where information is delayed, duplicated, or lost
- Which tasks exist only to compensate for unclear processes
- How operators adapt to gaps in procedures or systems
This phase is particularly important in environments such as hospitality, mixed-use developments, and large-scale communities, where security must remain effective without becoming intrusive.
Early intervention often creates instability. A disciplined assessment phase builds trust, reveals operational reality, and establishes the foundation required before introducing structured frameworks or enabling technologies such as PSIM.
Defining Normal Operations Before Managing Incidents
Most organizations start by planning for emergencies. A structured security operations approach PSIM starts somewhere else: by defining what “normal operations” actually look like.
If daily operations are unclear, incident response will fail under pressure. Teams cannot escalate consistently if they do not first agree on what standard operations should look like.
Before discussing major incidents, alignment must exist on:
- What constitutes a standard incident and how it is classified
- When escalation is required and based on which criteria
- Who owns decisions at each level of operation
- What information must be available and to whom
- What defines closure and how outcomes are recorded
This is where operational confidence begins. Once normal operations are clearly defined, escalation becomes structured instead of reactive, and coordination becomes predictable instead of personality-driven.
Only at this stage can systems such as PSIM support operations effectively, because the logic they rely on is already defined.
PSIM Security Operations Framework: People, Processes, and Technology
A structured security operations approach PSIM depends on the correct alignment of three core elements: people, processes, and technology. The sequence matters. When this order is reversed, complexity increases and consistency decreases.
The framework follows a clear progression:
- People — Roles, responsibilities, authority, and decision rights must be clearly defined.
- Processes — Practical workflows that guide incident handling, escalation, coordination, and reporting.
- Technology — Systems such as PSIM reinforce consistency and decision support.
Organizations that introduce technology first often experience fragmentation. A PSIM security operations framework ensures that technology amplifies a structured model rather than compensating for its absence.
This principle aligns with structured approaches such as the integrated operations center roadmap.
When PSIM Becomes Relevant in a Security Operations Approach
PSIM is often introduced too early. It becomes relevant only when operational clarity already exists.
- Incident categories are clearly defined
- Escalation logic is consistent
- Operators understand expected decisions
- Management knows required information
- A shared operational picture exists
When implemented correctly, PSIM becomes a force multiplier. When implemented too early, it amplifies confusion.
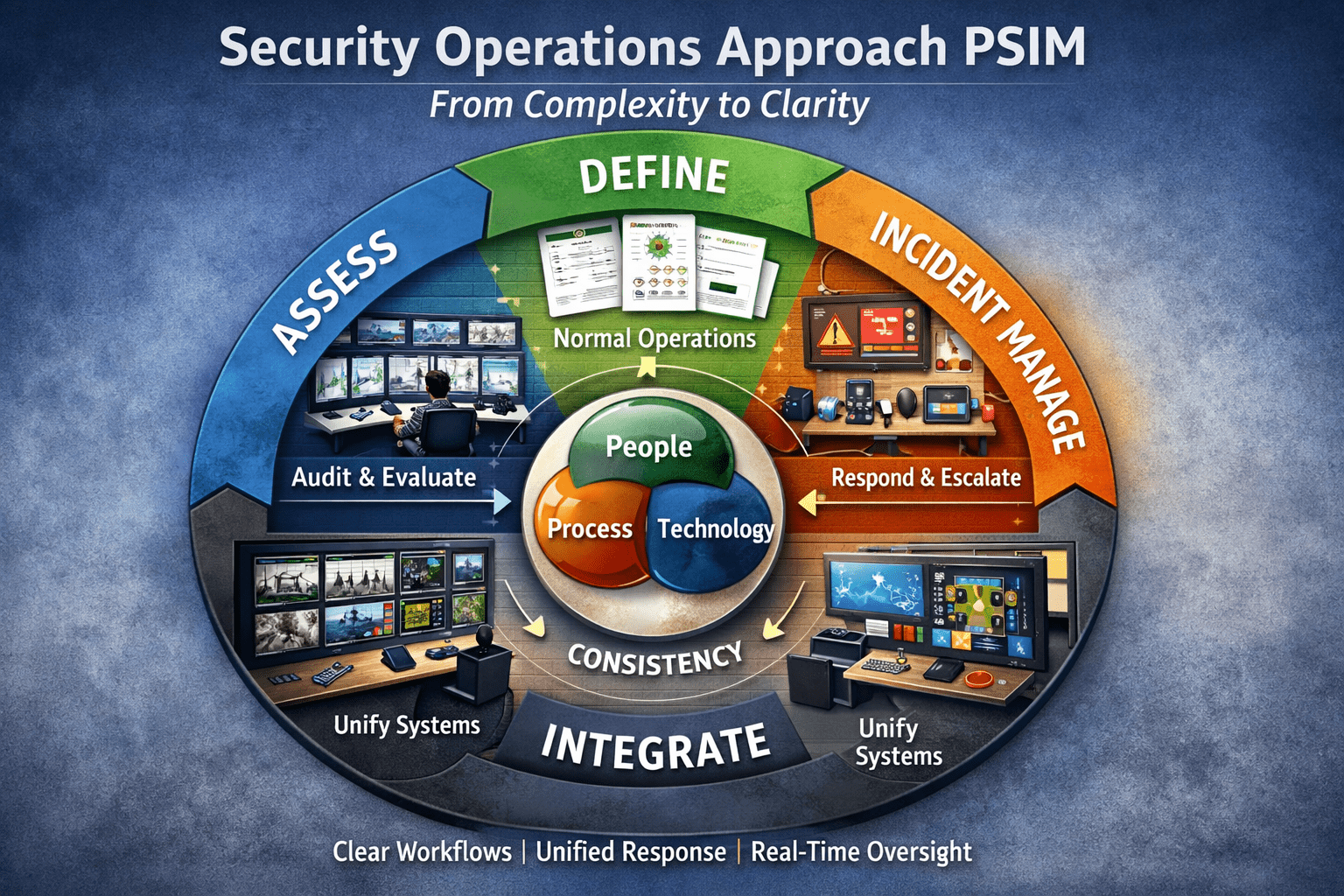
PSIM Incident Management Workflow
A mature security operations approach PSIM is reflected in how incidents are handled.
- Detection and validation
- Classification
- Escalation
- Coordination
- Closure and review
These steps are supported by response procedures and escalation workflows.
Consistency in workflow creates operational confidence and reliability.
How I Think About PSIM — Beyond Technology
In a structured security operations approach PSIM, PSIM is not defined by software. It is defined by how it supports decision-making.
I approach PSIM as an operational language that structures how incidents are understood and managed.
- Supports decisions
- Structures escalation
- Creates shared understanding
- Preserves operational knowledge
The value lies in consistency under pressure, not system integration alone.
PSIM platforms are tools that reinforce an already defined structure.
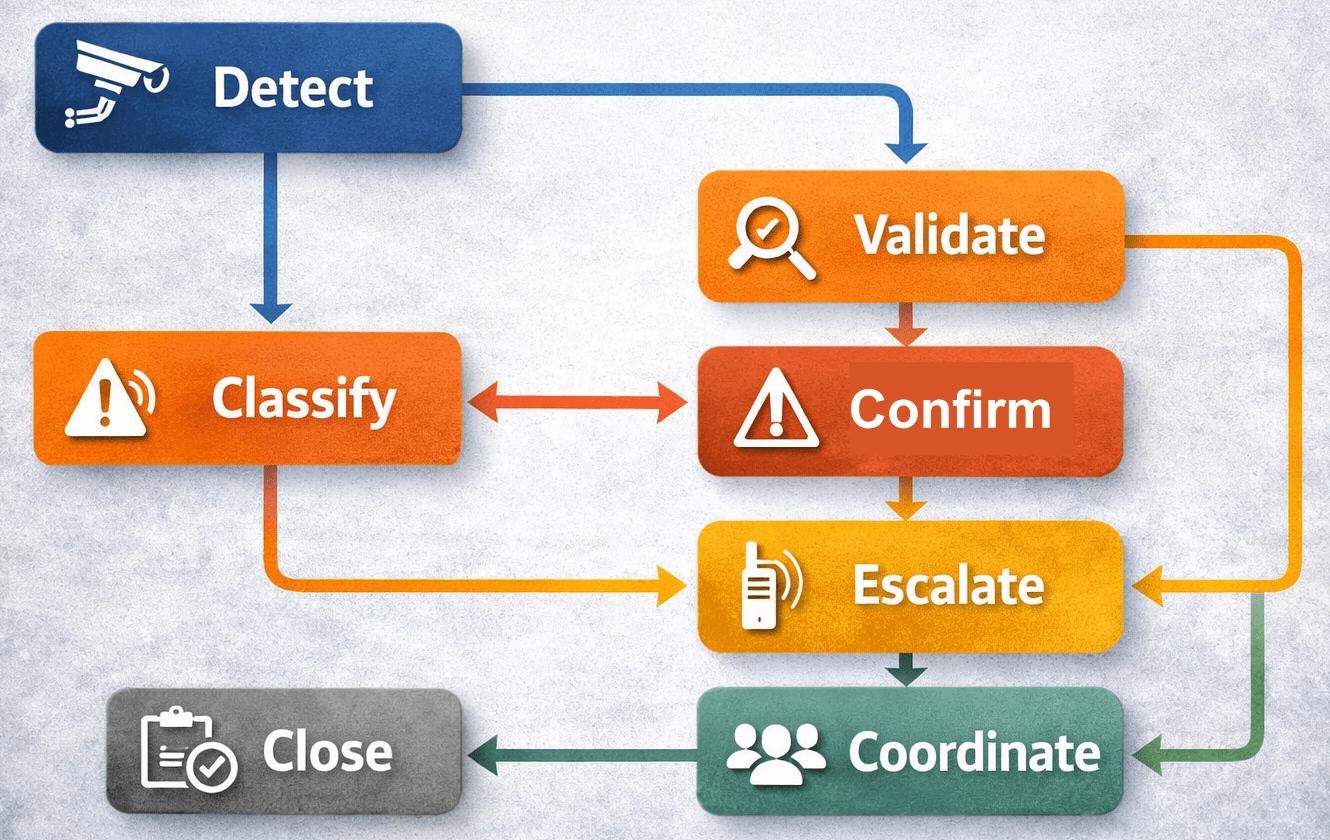
Integrated Security Operations Center Using PSIM
An integrated security operations center PSIM environment is where strategy, structure, and technology come together in real time.
In complex environments, security operations cannot function as isolated activities. Surveillance, access control, incident management, communications, and operational coordination must be aligned within a single operational framework.
A properly designed PSIM-enabled operations center provides:
- A shared operational picture across all stakeholders
- Real-time visibility of incidents, resources, and status
- Structured workflows that guide operators through decisions
- Coordinated communication between security, facilities, and external agencies
- Centralized oversight without losing local operational context
The objective is not centralization for its own sake. The objective is coordinated decision-making — ensuring that all actors operate from the same understanding of events and priorities.
This is particularly relevant in large-scale environments such as mixed-use developments, hospitality portfolios, and community operations, where multiple teams must respond simultaneously without creating operational friction.
When aligned with a structured operations center roadmap, PSIM enables integration without complexity and coordination without confusion.
One Security Operations Approach, Different Environments
A structured security operations approach PSIM is not limited to one type of environment. The core principles remain consistent, but the risk profile, operational priorities, and coordination requirements vary.
The strength of the approach lies in its ability to adapt without losing structure.
- Hospitality environments — Security must remain discreet while enabling rapid coordination. The focus is on guest experience, incident prevention, and seamless response without visible disruption.
- Community and mixed-use developments — Operations must scale across multiple stakeholders, assets, and risk types. Clear governance and shared operational understanding are critical.
- Construction projects — Dynamic conditions, evolving risks, and temporary setups require flexible but structured coordination. Procedures must adapt without losing clarity.
- Retail and mall environments — High density, constant activity, and frequent low-level incidents require consistent handling and strong situational awareness.
In each of these environments, PSIM supports coordination, but only when the operational model is clearly defined. The technology adapts to the environment — not the other way around.
This adaptability is what allows a structured security operations approach to remain effective across different scales, complexities, and operational contexts.
Why This Security Operations Approach Scales and Sustains Performance
A well-structured security operations approach PSIM is not only designed to function under pressure — it is designed to remain effective as organizations grow, change, and evolve.
Many security operations depend heavily on individuals who “know how things work.” While this may work in the short term, it creates fragility. When those individuals leave, consistency and confidence often disappear with them.
This approach focuses on building institutional capability rather than individual dependency.
- Defined decision structures — ensuring that actions are based on agreed criteria, not personal judgment
- Consistent workflows — enabling predictable handling of incidents across shifts and teams
- Shared operational understanding — reducing miscommunication and improving coordination
- Documented procedures and escalation logic — supporting continuity and training
- Technology that reinforces structure — with PSIM enabling visibility and coordination
As organizations expand — whether through additional assets, increased complexity, or higher risk exposure — this structure allows operations to scale without losing control.
It also ensures resilience during leadership changes, operational transitions, or unexpected disruptions. The system continues to function because it is built on defined principles rather than individual experience.
This is what transforms security operations from reactive activity into a reliable operational capability.
Why Organizations Engage Me to Improve Security Operations
I am typically engaged when security operations feel active but not effective — when systems are in place, teams are working, but clarity, consistency, and confidence are missing.
Organizations often reach this point after investing in technology that has not delivered the expected operational value, or when leadership needs a clearer understanding of how security decisions are actually made.
Common situations include:
- Security operations that appear busy but lack coordination
- Inconsistent incident handling across teams or shifts
- Technology platforms that generate data but do not support decisions
- Unclear escalation structures and decision ownership
- A need to prepare operations for integration through PSIM
My focus is not to introduce tools first, but to establish clarity, structure, and operational stability. Once this foundation is in place, organizations can confidently scale, integrate systems, and improve performance without increasing complexity.
This approach ensures that investments in areas such as PSIM are aligned with real operational needs rather than assumptions.
How I Can Support Your Security Operations
Many organizations invest heavily in systems and infrastructure, yet still struggle with clarity, coordination, and consistent decision-making. In most cases, the challenge is not technology — it is the absence of a structured operational model.
If you are looking to strengthen your security operations approach PSIM, I provide independent, practical support focused on operational clarity and readiness. This includes:
- Concept of Operations (ConOps) development
- Security operations framework design
- Incident management and escalation models
- Procedure development aligned with real operations
- PSIM readiness assessments and integration support
- Operational reviews and structured improvement plans
The objective is not to introduce complexity, but to create a clear, structured environment where teams can operate confidently and systems deliver real value.
If you would like to discuss your current setup, challenges, or upcoming projects, you can reach out confidentially.
Frequently Asked Questions About Security Operations Approach PSIM
What is a security operations approach PSIM?
A security operations approach PSIM is a structured method of managing security through integrated systems, defined processes, and coordinated decision-making. It aligns people, procedures, and technology to ensure consistent incident handling and operational clarity.
When should PSIM be implemented in security operations?
PSIM should be implemented only after operational foundations are clearly defined. This includes incident classification, escalation logic, and decision-making structures. Introducing PSIM too early often increases complexity instead of improving coordination.
What are the benefits of using PSIM in a security operations center?
PSIM improves coordination, situational awareness, and decision-making by integrating multiple systems into a single operational environment. It enables consistent workflows, faster response times, and better communication across teams and stakeholders.
What is a PSIM incident management workflow?
A PSIM incident management workflow is a structured process that includes detection, validation, classification, escalation, coordination, and closure of incidents. It ensures that incidents are handled consistently regardless of who is on duty.
How does PSIM support integrated security operations?
PSIM supports integrated security operations by connecting systems such as CCTV, access control, and alarms into one platform. It provides a shared operational picture and enables coordinated responses across multiple teams and functions.
What is the biggest mistake when implementing PSIM?
The most common mistake is implementing PSIM before defining operational processes and governance. Without clear workflows and decision structures, PSIM becomes a complex interface rather than a tool that improves coordination and efficiency.
How do you prepare for PSIM implementation?
Preparation involves defining incident categories, escalation logic, roles and responsibilities, and operational workflows. Organizations should ensure that decision-making processes are clear before introducing PSIM as an enabling technology.
Can PSIM replace security personnel or decision-making?
No. PSIM is designed to support decision-making, not replace it. It provides structure, visibility, and coordination tools, but effective security operations still depend on trained personnel and clear operational frameworks.
Key Takeaways
- A security operations approach PSIM is built on structure, not technology.
- Operational clarity must be established before introducing systems or integrations.
- Defining normal operations is the foundation for consistent incident management.
- PSIM becomes effective only when roles, processes, and decision logic are clearly defined.
- A structured incident workflow ensures consistent handling from detection to closure.
- Integrated operations centers enable coordinated decision-making across multiple stakeholders.
- Well-designed security operations scale, adapt, and remain effective under pressure.
Conclusion
A security operations approach PSIM is not defined by technology, but by how clearly operations are structured, understood, and executed under real conditions.
From assessing existing operations and defining normal workflows, to aligning people, processes, and technology, each stage builds the foundation required for consistent and effective decision-making.
PSIM plays a critical role in this model, but only when introduced at the right time. As an operational enabler, it reinforces structure, supports coordination, and enhances visibility across complex environments.
Organizations that focus on clarity before integration achieve more than improved performance. They build security operations that are scalable, resilient, and trusted.
Ultimately, the objective is not to implement systems, but to create a predictable, structured, and confident operational capability — one that performs consistently regardless of complexity or pressure.
Disclaimer: This content is informational and does not constitute legal advice. Regulatory requirements and licensing conditions differ by jurisdiction and must be confirmed for each site.